Contents
- 1 The growing threat of cyber attacks and data breaches
- 2 The impact of data breaches on businesses and individuals
- 3 Laws and regulations protecting data privacy and cybersecurity
- 4 Steps to protect personal and business data
- 5 The role of encryption in data privacy and cybersecurity
- 6 Importance of cybersecurity training and awareness
- 7 The future of data privacy and cybersecurity
- 8 Key players in the data privacy and cybersecurity industry
- 9 Conclusion
- 10 Author
In today’s digital age, data privacy and cybersecurity are becoming increasingly important. With the rapid advancement of technology and the widespread use of the internet, our personal information is now more vulnerable than ever before. Cybercriminals and hackers are constantly finding new ways to exploit weaknesses in our digital infrastructure, putting our sensitive data at risk.
The growing threat of cyber attacks and data breaches
Cyber attacks and data breaches have become a major concern in recent years. The frequency and sophistication of these attacks have increased, leaving individuals and businesses exposed to significant risks. Cybercriminals employ various tactics such as phishing, malware, ransomware, and social engineering to gain unauthorized access to personal and sensitive information.
These attacks can have devastating consequences, both financially and emotionally. For individuals, a data breach can lead to identity theft, financial loss, and damage to their online reputation. Businesses, on the other hand, can suffer from reputational damage, loss of customer trust, and hefty financial penalties.
To combat this growing threat, it is essential for individuals and businesses to invest in robust cybersecurity measures. This includes implementing firewalls, antivirus software, and encryption protocols to protect sensitive data. Regular security audits and penetration testing can also help identify vulnerabilities and prevent potential breaches.
The impact of data breaches on businesses and individuals
The impact of a data breach can be far-reaching, affecting both businesses and individuals. For businesses, the financial implications can be significant. The cost of investigating and remedying a breach, as well as potential legal fees and fines, can cripple a company’s finances. Moreover, the damage to reputation and loss of customer trust can have long-lasting effects on the success and sustainability of the business.
For individuals, the consequences of a data breach can be equally devastating. Stolen personal information can be used for identity theft, leading to financial fraud and damage to one’s credit score. The emotional toll of having one’s privacy violated can also be immense, causing stress, anxiety, and a loss of trust in online services.
It is crucial for businesses to prioritize data privacy and cybersecurity to protect their customers’ personal information. Implementing secure systems, conducting regular security audits, and providing cybersecurity awareness training to employees can help mitigate the risks of a data breach and safeguard sensitive data.
Laws and regulations protecting data privacy and cybersecurity
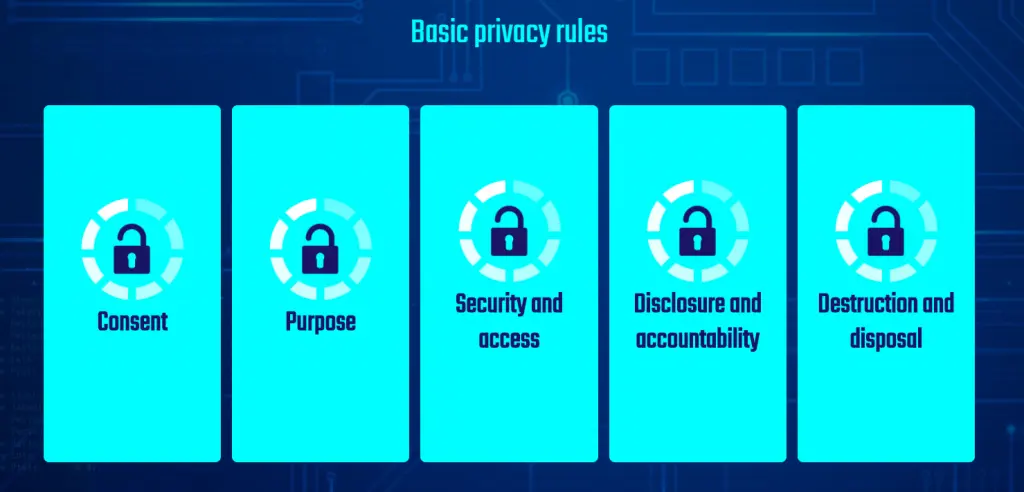
Recognizing the importance of data privacy and cybersecurity, governments around the world have implemented laws and regulations to protect individuals and businesses. For instance, the European Union’s General Data Protection Regulation (GDPR) sets strict guidelines for the collection, storage, and processing of personal data. Non-compliance with these regulations can result in hefty fines.
Similarly, the California Consumer Privacy Act (CCPA) aims to enhance privacy rights and consumer protection for residents of California. It provides individuals with the right to know what personal information is being collected and how it is being used, as well as the right to opt-out of the sale of their personal information.
These laws and regulations serve as a framework for businesses to ensure they are handling personal data in a responsible and secure manner. By complying with these regulations, businesses not only protect themselves from legal consequences but also establish trust and credibility with their customers.
Steps to protect personal and business data
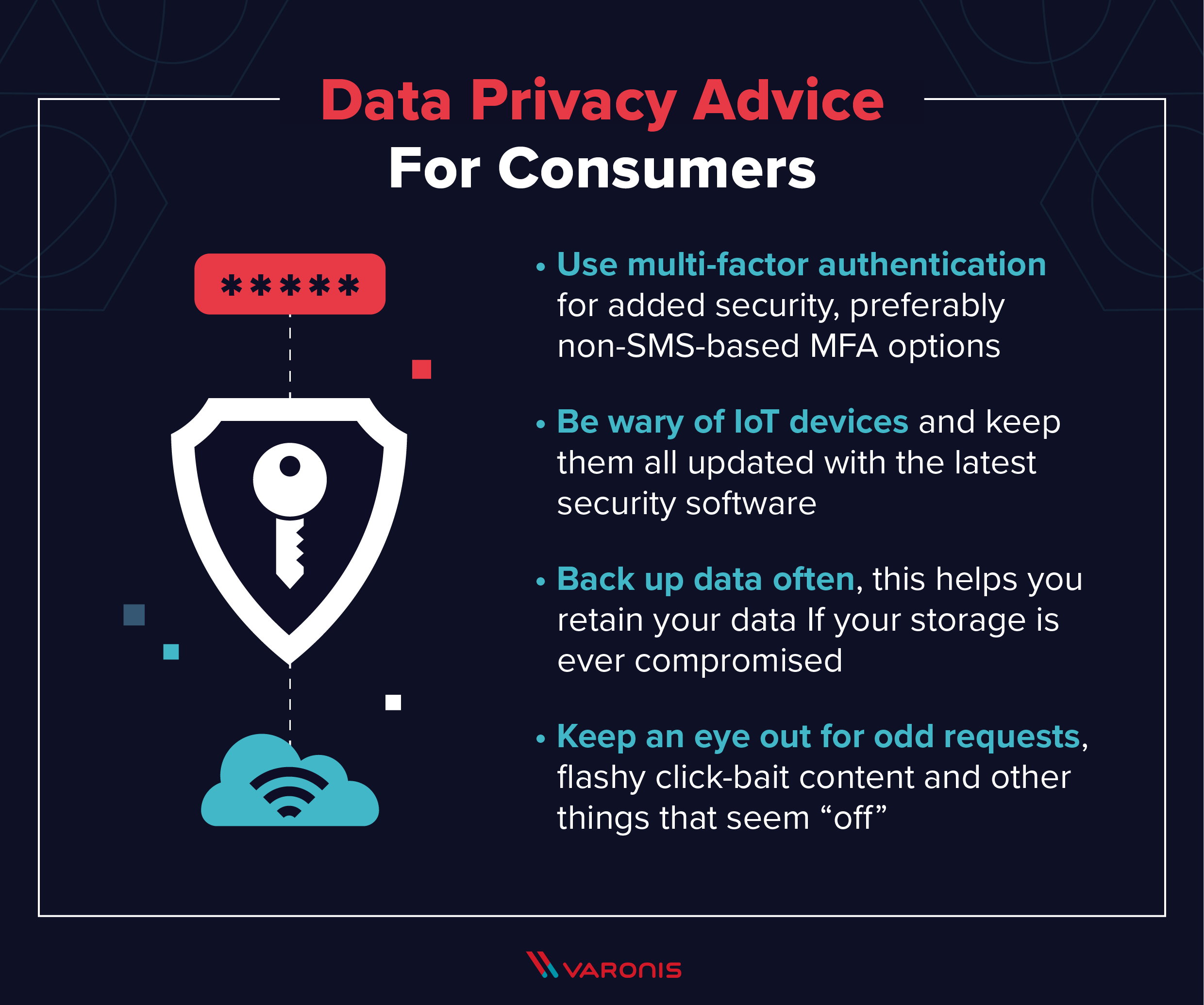
Protecting personal and business data requires a proactive approach. Here are some essential steps that individuals and businesses can take to enhance their data privacy and cybersecurity:
- Keep software and devices updated: Regularly update software and devices with the latest security patches to protect against known vulnerabilities.
- Use strong and unique passwords: Avoid using easily guessable passwords and consider using a password manager to securely store and generate unique passwords for different accounts.
- Enable two-factor authentication (2FA): Implement 2FA whenever possible to add an extra layer of security to online accounts.
- Be cautious of phishing attempts: Be vigilant when opening emails or clicking on links, especially from unfamiliar sources. Avoid providing personal information or clicking on suspicious links.
- Regularly back up data: Keep regular backups of important data and store them securely offline or using cloud storage with strong encryption.
- Encrypt sensitive information: Utilize encryption technologies to protect sensitive data, both in transit and at rest.
- Train employees in cybersecurity best practices: Educate employees about cybersecurity risks, such as social engineering and phishing, and provide training on how to identify and respond to potential threats.
- Monitor and detect suspicious activity: Implement robust monitoring systems to detect and respond to any unusual activity that may indicate a potential breach.
By following these steps, individuals and businesses can significantly reduce the risk of falling victim to a data breach and protect their valuable data.
The role of encryption in data privacy and cybersecurity
Encryption plays a crucial role in data privacy and cybersecurity. It involves encoding data in such a way that it can only be accessed or decrypted by authorized parties. Encryption ensures that even if data is intercepted or stolen, it remains unreadable and unusable to unauthorized individuals.
There are various encryption methods available, such as symmetric encryption, asymmetric encryption, and hashing algorithms. Each method has its own strengths and weaknesses, and the choice of encryption method depends on the specific use case and desired level of security.
Encryption is widely used to protect sensitive data during transmission over networks, such as when making online transactions or accessing secure websites. It is also used to secure data stored on devices, such as laptops, smartphones, and servers.
Implementing encryption is an essential component of any data privacy and cybersecurity strategy. By encrypting sensitive data, individuals and businesses can ensure that their information remains confidential and protected from unauthorized access.
Importance of cybersecurity training and awareness
While implementing robust cybersecurity measures is crucial, it is equally important to educate individuals and employees about cybersecurity best practices. Cybersecurity training and awareness programs can help individuals recognize potential threats, understand the importance of data privacy, and learn how to protect themselves and their organizations from cyber attacks.
Employees are often the first line of defense against cyber threats, and their actions can significantly impact the security posture of an organization. By training employees on topics such as phishing awareness, password hygiene, and safe internet browsing, businesses can strengthen their overall cybersecurity resilience.
Furthermore, individuals should also stay informed about the latest cybersecurity trends and best practices. Regularly updating knowledge on emerging threats, new attack vectors, and evolving technologies can help individuals make informed decisions and stay one step ahead of cybercriminals.
The future of data privacy and cybersecurity
As technology continues to advance, the landscape of data privacy and cybersecurity will continue to evolve. The increasing interconnectedness of devices and the proliferation of the Internet of Things (IoT) pose new challenges and risks to data privacy and cybersecurity.
Emerging technologies such as artificial intelligence (AI), machine learning, and blockchain offer both opportunities and challenges in the context of data privacy and cybersecurity. AI and machine learning can help identify patterns and anomalies in network traffic, enabling faster detection and response to cyber threats. However, they can also be used by cybercriminals to launch more sophisticated attacks.
Blockchain technology, on the other hand, offers the potential for decentralized and tamper-proof data storage and transactions. It can enhance data privacy by giving individuals more control over their personal information. However, as with any technology, there are also concerns and challenges associated with blockchain, such as scalability and regulatory frameworks.
The future of data privacy and cybersecurity will require continuous innovation, collaboration, and adaptation to stay ahead of cyber threats. It will be essential for individuals, businesses, and governments to work together to develop and implement effective strategies to protect sensitive data and ensure a secure digital environment.
Key players in the data privacy and cybersecurity industry
The data privacy and cybersecurity industry is vast and comprises various organizations, professionals, and technologies. Some key players in the industry include:
- Cybersecurity companies: These companies specialize in providing cybersecurity solutions, such as antivirus software, firewalls, and intrusion detection systems. Examples include Symantec, McAfee, and Palo Alto Networks.
- Consulting firms: Consulting firms offer cybersecurity consulting services, helping businesses assess their security posture, develop cybersecurity strategies, and implement security controls. Deloitte, PwC, and KPMG are some prominent examples.
- Technology vendors: Technology vendors provide hardware and software solutions that enhance data privacy and cybersecurity. This includes encryption software, network security appliances, and secure communication platforms. Companies like Cisco, IBM, and Microsoft are leaders in this space.
- Government agencies: Governments play a crucial role in shaping data privacy and cybersecurity policies and regulations. Agencies such as the National Institute of Standards and Technology (NIST) in the United States and the National Cyber Security Centre (NCSC) in the United Kingdom provide guidelines and resources to businesses and individuals.
- Educational institutions: Universities and research institutions conduct research and offer education and training programs in the field of cybersecurity. Their work contributes to the development of new technologies and the cultivation of skilled professionals in the industry.
These key players, along with many others, collaborate to address the evolving challenges and threats in the data privacy and cybersecurity landscape.
Conclusion
In conclusion, data privacy and cybersecurity have become increasingly important in the digital age. The growing threat of cyber attacks and data breaches necessitates a proactive approach to protect personal and business data. Laws and regulations provide a framework for ensuring data privacy and cybersecurity, and encryption plays a crucial role in safeguarding sensitive information.
By prioritizing cybersecurity training and awareness, individuals and businesses can enhance their resilience against cyber threats. The future of data privacy and cybersecurity will require continuous innovation and collaboration, and key players in the industry will play a vital role in shaping the landscape.
As we navigate the digital landscape, it is imperative that we remain vigilant and take the necessary steps to protect our personal information and maintain a secure online presence. By understanding the risks associated with data privacy and cybersecurity, we can navigate the digital age with confidence and ensure the safety and privacy of our valuable data.
If you found this article insightful and wish to explore more intriguing topics, we invite you to delve into our article covering the exciting events and highlights of Coachella 2024. Whether you’re interested in cybersecurity or looking forward to the latest music and entertainment experiences, we have a diverse range of content to cater to your interests.




